-->
- Adobe Type Manager Deluxe Download
- Adobe Type Manager
- Adobe Type Manager For Windows 7 64-bit
- Adobe Type Manager Virus
- Adobe Type Manager Atmfd
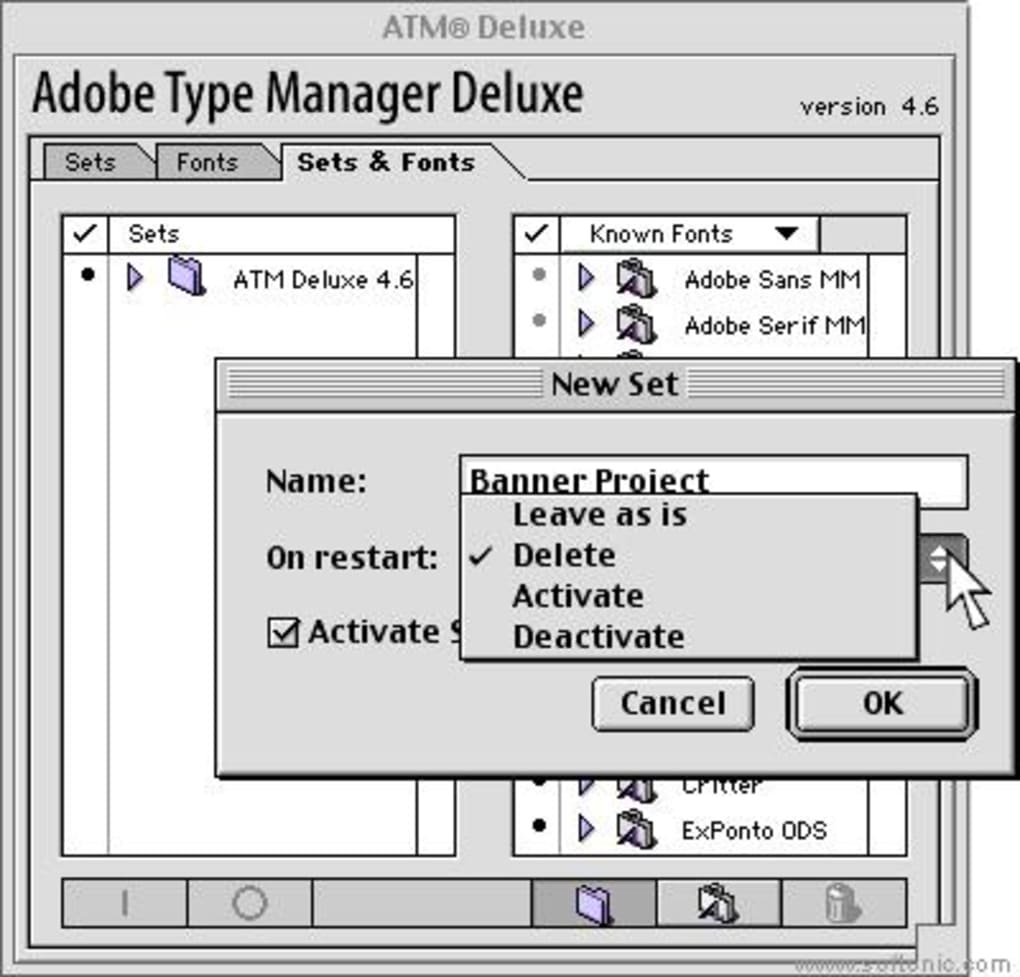
Adobe Type Manager is an OpenType and PostScript font manager, that as well as allowing us to open this kind of fonts, will make it easier for us to organize and print them. The program has a very simple interface, from which we can add fonts to a list, so that we can later group them and be able to access them in a more simple way. Adobe Type Manager. According to our registry, Adobe Type Manager is capable of opening the files listed below. It is possible that Adobe Type Manager can convert between the listed formats as well, the application’s manual can provide information about it. Adobe Type Manager (ATM) Light is a system software component that automatically generates high-quality screen font bitmaps from the PostScript outlines in Type 1 or OpenType format. ATM Light was discontinued in 2005, but Adobe still makes it available for customers who require it for older operating systems. An elevation of privilege vulnerability exists in Adobe Type Manager Font Driver (ATMFD) when it fails to properly handle objects in memory. An attacker who successfully exploited this vulnerability could execute arbitrary code and take complete control of an affected system.
Vulnerability in ATM Font Driver Could Allow Elevation of Privilege (3077657)
Published: July 14, 2015
Version: 1.0
Executive Summary
This security update resolves a vulnerability in Microsoft Windows. The vulnerability could allow elevation of privilege if an attacker logs on to a target system and runs a specially crafted application. An attacker who successfully exploited this vulnerability could execute arbitrary code and take complete control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
This security update is rated Important for all supported releases of Microsoft Windows. For more information, see the Affected Software section.
The security update addresses the vulnerability by correcting how Adobe Type Manager Font Driver (ATMFD) handles objects in memory. For more information about the vulnerability, see the Vulnerability Information section.
For more information about this update, see Microsoft Knowledge Base Article 3077657.
Affected Software
The following software versions or editions are affected. Versions or editions that are not listed are either past their support life cycle or are not affected. To determine the support life cycle for your software version or edition, see Microsoft Support Lifecycle.
| **Operating System** | **Maximum Security Impact** | **Aggregate Severity Rating** | **Updates Replaced** |
| **Windows Server 2003** | |||
| [Windows Server 2003 Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=742f6b42-c129-49d2-a1d2-cdead3adf1d2) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| [Windows Server 2003 x64 Edition Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=2b8be95e-b2b5-49e8-8356-d486b126a1d4) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| [Windows Server 2003 with SP2 for Itanium-based Systems](https://www.microsoft.com/download/details.aspx?familyid=a327422c-5a1c-4f33-a340-7139967f4aeb) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| **Windows Vista** | |||
| [Windows Vista Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=56fb37c2-89f2-428f-99f6-7f93ca3b6466) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| [Windows Vista x64 Edition Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=c9d53542-c59a-4eb1-a07d-1deaf4e8ddd4) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| **Windows Server 2008** | |||
| [Windows Server 2008 for 32-bit Systems Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=f8e85e7d-901f-487f-82af-66a6f370227b) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| [Windows Server 2008 for x64-based Systems Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=ece6dfdf-a0e6-43d6-a251-3ac97ec01e1c) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| [Windows Server 2008 for Itanium-based Systems Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=aa38cd25-e828-494b-bf9b-7444737630de) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| **Windows 7** | |||
| [Windows 7 for 32-bit Systems Service Pack 1](https://www.microsoft.com/download/details.aspx?familyid=dce5e481-d161-4b0d-a84e-a199859be2c9) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| [Windows 7 for x64-based Systems Service Pack 1](https://www.microsoft.com/download/details.aspx?familyid=b0a49f6a-cfd1-4360-a1d3-485fcd1c03d7) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| **Windows Server 2008 R2** | |||
| [Windows Server 2008 R2 for x64-based Systems Service Pack 1](https://www.microsoft.com/download/details.aspx?familyid=2ea53897-d9cf-4265-9da3-2c6142ebf497) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| [Windows Server 2008 R2 for Itanium-based Systems Service Pack 1](https://www.microsoft.com/download/details.aspx?familyid=6955ec86-8382-4a53-b75f-68b59bf96725) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| **Windows 8 and Windows 8.1** | |||
| [Windows 8 for 32-bit Systems](https://www.microsoft.com/download/details.aspx?familyid=0ec2b082-752b-4470-b988-56200d2c1561) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| [Windows 8 for x64-based Systems](https://www.microsoft.com/download/details.aspx?familyid=ca256d0e-057b-4c4b-bf35-88d18a28ad44) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| [Windows 8.1 for 32-bit Systems](https://www.microsoft.com/download/details.aspx?familyid=ac718319-e2bf-491c-9af9-b17f9816f294) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| [Windows 8.1 for x64-based Systems](https://www.microsoft.com/download/details.aspx?familyid=15c3ebf6-f4fc-45ad-9b6c-059bf2fcf4b5) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| **Windows Server 2012 and Windows Server 2012 R2** | |||
| [Windows Server 2012](https://www.microsoft.com/download/details.aspx?familyid=6540a761-fd9f-49f1-a1e9-c50c7d73e242) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| [Windows Server 2012 R2](https://www.microsoft.com/download/details.aspx?familyid=9c6e30e9-b022-4d8e-9aa5-a702d9f76aa4) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| **Windows RT and Windows RT 8.1** | |||
| Windows RT[1](3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| Windows RT 8.1[1](3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| **Server Core installation option** | |||
| [Windows Server 2008 for 32-bit Systems Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=f8e85e7d-901f-487f-82af-66a6f370227b) (Server Core installation) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| [Windows Server 2008 for x64-based Systems Service Pack 2](https://www.microsoft.com/download/details.aspx?familyid=ece6dfdf-a0e6-43d6-a251-3ac97ec01e1c) (Server Core installation) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| [Windows Server 2008 R2 for x64-based Systems Service Pack 1](https://www.microsoft.com/download/details.aspx?familyid=2ea53897-d9cf-4265-9da3-2c6142ebf497) (Server Core installation) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| [Windows Server 2012](https://www.microsoft.com/download/details.aspx?familyid=6540a761-fd9f-49f1-a1e9-c50c7d73e242) (Server Core installation) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
| [Windows Server 2012 R2](https://www.microsoft.com/download/details.aspx?familyid=9c6e30e9-b022-4d8e-9aa5-a702d9f76aa4) (Server Core installation) (3077657) | Elevation of Privilege | Important | 3032323 in [MS15-021](http://go.microsoft.com/fwlink/?linkid=526457) |
*The Updates Replaced column shows only the latest update in a chain of superseded updates. For a comprehensive list of updates replaced, go to the Microsoft Update Catalog, search for the update KB number, and then view update details (updates replaced information is on the Package Details tab).
Severity Ratings and Vulnerability Identifiers
The following severity ratings assume the potential maximum impact of the vulnerability. For information regarding the likelihood, within 30 days of this security bulletin's release, of the exploitability of the vulnerability in relation to its severity rating and security impact, please see the Exploitability Index in the July bulletin summary.
| **Vulnerability Severity Rating and Maximum Security Impact by Affected Software** | ||
| **Affected Software** | [**ATMFD.DLL Memory Corruption Vulnerability - CVE-2015-2387**](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2015-2387) | **Aggregate Severity Rating** |
| **Windows Server 2003** | ||
| Windows Server 2003 Service Pack 2 (3077657) | **Important** Elevation of Privilege | **Important** |
| Windows Server 2003 x64 Edition Service Pack 2 (3077657) | **Important** Elevation of Privilege | **Important** |
| Windows Server 2003 with SP2 for Itanium-based Systems (3077657) | **Important** Elevation of Privilege | **Important** |
| **Windows Vista** | ||
| Windows Vista Service Pack 2 (3077657) | **Important** Elevation of Privilege | **Important** |
| Windows Vista x64 Edition Service Pack 2 (3077657) | **Important** Elevation of Privilege | **Important** |
| **Windows Server 2008** | ||
| Windows Server 2008 for 32-bit Systems Service Pack 2 (3077657) | **Important** Elevation of Privilege | **Important** |
| Windows Server 2008 for x64-based Systems Service Pack 2 (3077657) | **Important** Elevation of Privilege | **Important** |
| Windows Server 2008 for Itanium-based Systems Service Pack 2 (3077657) | **Important** Elevation of Privilege | **Important** |
| **Windows 7** | ||
| Windows 7 for 32-bit Systems Service Pack 1 (3077657) | **Important** Elevation of Privilege | **Important** |
| Windows 7 for x64-based Systems Service Pack 1 (3077657) | **Important** Elevation of Privilege | **Important** |
| **Windows Server 2008 R2** | ||
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 (3077657) | **Important** Elevation of Privilege | **Important** |
| Windows Server 2008 R2 for Itanium-based Systems Service Pack 1 (3077657) | **Important** Elevation of Privilege | **Important** |
| **Windows 8 and Windows 8.1** | ||
| Windows 8 for 32-bit Systems (3077657) | **Important** Elevation of Privilege | **Important** |
| Windows 8 for x64-based Systems (3077657) | **Important** Elevation of Privilege | **Important** |
| Windows 8.1 for 32-bit Systems (3077657) | **Important** Elevation of Privilege | **Important** |
| Windows 8.1 for x64-based Systems (3077657) | **Important** Elevation of Privilege | **Important** |
| **Windows Server 2012 and Windows Server 2012 R2** | ||
| Windows Server 2012 (3077657) | **Important** Elevation of Privilege | **Important** |
| Windows Server 2012 R2 (3077657) | **Important** Elevation of Privilege | **Important** |
| **Windows RT and Windows RT 8.1** | ||
| Windows RT[1](3077657) | **Important** Elevation of Privilege | **Important** |
| Windows RT 8.1[1](3077657) | **Important** Elevation of Privilege | **Important** |
| **Server Core installation option** | ||
| Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) (3077657) | **Important** Elevation of Privilege | **Important** |
| Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) (3077657) | **Important** Elevation of Privilege | **Important** |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation) (3077657) | **Important** Elevation of Privilege | **Important** |
| Windows Server 2012 (Server Core installation) (3077657) | **Important** Elevation of Privilege | **Important** |
| Windows Server 2012 R2 (Server Core installation) (3077657) | **Important** Elevation of Privilege | **Important** |
Vulnerability Information
ATMFD.DLL Memory Corruption Vulnerability - CVE-2015-2387
An elevation of privilege vulnerability exists in Adobe Type Manager Font Driver (ATMFD) when it fails to properly handle objects in memory. An attacker who successfully exploited this vulnerability could execute arbitrary code and take complete control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
To exploit the vulnerability, an attacker would first have to log on to a target system and then run a specially crafted application. The security update addresses the vulnerability by correcting how ATMFD handles objects in memory.
This vulnerability has been publicly disclosed. It has been assigned Common Vulnerability and Exposure number CVE-2015-2387. When this bulletin was originally released, Microsoft was aware of limited, targeted attacks that attempt to exploit this vulnerability.
Mitigating Factors
Microsoft has not identified any mitigating factors for this vulnerability.
Workarounds
The following workarounds may be helpful in your situation:
Rename ATMFD.DLL Note This workaround is applicable to all operating systems except Windows Server 2003 due to active file protection. See Microsoft Knowledge Base Article 222193 for more information
For 32-bit systems:
Enter the following commands at an administrative command prompt:
Restart the system.
For 64-bit systems:
Enter the following commands at an administrative command prompt:
Restart the system.
Optional procedure for Windows 8 and newer systems (disable ATMFD):
Note Using Registry Editor incorrectly can cause serious problems that may require you to reinstall your operating system. Microsoft cannot guarantee that problems resulting from the incorrect use of Registry Editor can be solved. Use Registry Editor at your own risk. For information about how to edit the registry, view the 'Changing Keys And Values' Help topic in Registry Editor (Regedit.exe) or view the 'Add and Delete Information in the Registry' and 'Edit Registry Data' Help topics in Regedt32.exe.
Method 1 (manually edit the system registry):
Run regedit.exe as Administrator.
In Registry Editor, navigate to the following sub key (or create it) and set its DWORD value to 1:
HKLMSoftwareMicrosoftWindows NTCurrentVersionWindowsDisableATMFD, DWORD = 1
Close Registry Editor and restart the system.
Method 2 (use a managed deployment script):
Create a text file named ATMFD-disable.reg that contains the following text:
Run regedit.exe.
In Registry Editor, click the File menu and then click Import.
Navigate to and select the ATMFD-disable.reg file that you created in the first step.(Note If your file is not listed where you expect it to be, ensure that it has not been automatically given a .txt file extension, or change the dialog’s file extension parameters to All Files).
Click Open and then click OK to close Registry Editor.
Impact of workaround. Applications that rely on embedded font technology will not display properly.
How to undo the workaround.
For 32-bit systems:
Enter the following commands at an administrative command prompt:
Restart the system.
For 64-bit systems:
Enter the following commands at an administrative command prompt:
Restart the system.
Optional procedure for Windows 8 and newer systems (enable ATMFD):
Method 1 (manually edit the system registry):
Run regedit.exe as Administrator.
In Registry Editor, navigate to the following sub key and set its DWORD value to 0:
HKLMSoftwareMicrosoftWindows NTCurrentVersionWindowsDisableATMFD, DWORD = 0
Close Registry Editor and restart the system.
Method 2 (use a managed deployment script):
Create a text file named ATMFD-enable.reg that contains the following text:
Run regedit.exe.
In Registry Editor, click the File menu and then click Import.
Navigate to and select the ATMFD-enable.reg file that you created in the first step.(Note If your file is not listed where you expect it to be, ensure that it has not been automatically given a .txt file extension, or change the dialog’s file extension parameters to All Files).
Click Open and then click OK to close Registry Editor.
Security Update Deployment
For Security Update Deployment information, see the Microsoft Knowledge Base article referenced in the Executive Summary.
Acknowledgments
Microsoft recognizes the efforts of those in the security community who help us protect customers through coordinated vulnerability disclosure. See Acknowledgments for more information.
Disclaimer
The information provided in the Microsoft Knowledge Base is provided 'as is' without warranty of any kind. Microsoft disclaims all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. In no event shall Microsoft Corporation or its suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits or special damages, even if Microsoft Corporation or its suppliers have been advised of the possibility of such damages. Some states do not allow the exclusion or limitation of liability for consequential or incidental damages so the foregoing limitation may not apply.
Revisions
- V1.0 (July 14, 2015): Bulletin published.
Page generated 2015-07-20 11:42Z-07:00.
There are 22 other file types using
the LST file extension!
.lst - List text [common]
.lst - Oracle spool
.lst - Pro/ENGINEER temporary data
.lst - BPM Studio playlist file
.lst - Family Tree Maker error log
.lst - IMail Server List Server mail file
.lst - Ingres dump list file
.lst - Kaspersky Lab blacklist
.lst - Orchida knitting system data
.lst - Microsoft PowerPoint playlist
.lst - SAS procedure output file
.lst - SignIQ field list
.lst - Valve map related data
.lst - Microsoft Visual Studio MASM listing data
.lst - Alan Map 500 map list
.lst - Holux MapShow map list
.lst - Microsoft Visual FoxPro Documenting Wizard list file
.lst - LightScribe Template Labeler template file
.lst - ALSee thumbnail cache
.lst - Now Contact template
.lst - GNU GRUB boot list
.lst - GCC Assembler listing data
Bookmark & share this page with others:
LST file extension- Adobe Type Manager font list
What is lst file? How to open lst files?
File type specification:
lst file icon:
The lst file extension used by Adobe Type Manager, an application for Microsoft Windows and Apple Mac computers that allows users to work with Adobe Type 1 fonts.
The lst file stores font list.
This lst file type entry was marked as obsolete and no longer supported file format.
This type of file is no longer actively used and is most likely obsolete. This is typically the case for system files in old operating systems, file types from long discontinued software, or previous versions of certain file types (like documents, projects etc.) that were replaced in higher versions of their original programs.
The default software associated to open lst file:
Company or developer:
Adobe Systems Incorporated
Adobe Type Manager (ATM) is used to generate high-quality screen font bitmaps from the PostScript outlines in Type 1 or OpenType format. It is discontinued product.
Company or developer:
Adobe Systems Incorporated
Adobe Type Manager (ATM) is used to generate high-quality screen font bitmaps from the PostScript outlines in Type 1 or OpenType format. It is discontinued product that was also available for Mac.
Help how to open:
The lst files are used for internal purposes of Adobe Type Manager. May can be viewed in any text editor.
How to convert:
Adobe Type Manager Deluxe Download
Conversion to other formats is not possible.
List of software applications associated to the .lst file extension
Adobe Type Manager
Recommended software programs are sorted by OS platform (Windows, macOS, Linux, iOS, Android etc.)
and possible program actions that can be done with the file: like open lst file, edit lst file, convert lst file, view lst file, play lst file etc. (if exist software for corresponding action in File-Extensions.org's database).
Hint:
Click on the tab below to simply browse between the application actions, to quickly get a list of recommended software, which is able to perform the specified software action, such as opening, editing or converting lst files.
Programs that can create lst file - Adobe Type Manager font list
Adobe Type Manager For Windows 7 64-bit
Programs supporting the exension lst on the main platforms Windows, Mac, Linux or mobile. Click on the link to get more information about listed programs for create lst file action.